Tech
CISA warns of hackers exploiting Chrome, EoL D-Link bugs

The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has added three security vulnerabilities to its ‘Known Exploited Vulnerabilities’ catalog, one impacting Google Chrome and two affecting some D-Link routers.
Adding the issues to the KEV catalog serves as a warning to federal agencies and companies that threat actors are leveraging them in attacks and security updates or mitigations should be applied.
Federal agencies in the U.S. have until June 6th to replace affected devices or implement defenses that reduce or eliminate the risk of an attack.
Actively exploited flaws
The vulnerability in Google Chrome, tracked as CVE-2024-4761, has been confirmed by the vendor as actively exploited on May 13th but no technical details is currently publicly available.
It is described as an out of bounds write vulnerability in Chrome’s V8 JavaScript engine that executes JS code in the browser and its severity rating is high.
Two days after disclosing CVE-2024-4761 Google announced that another vulnerability (CVE-2024-4947) in Chrome’s V8 engine has been exploited in the wild, but CISA has yet to add it to the KEV catalog.
CISA is also warning that a ten-year old vulnerability impacting D-Link DIR-600 routers is still being exploited. The flaw is identified as CVE-2014-100005 and is a cross-site request forgery (CSRF) issue.
It allows attackers to hijack administrator authentication requests to the device’s web admin panel, create their own admin accounts, change the configuration, and take control of the device.
Although D-Link DIR-600 routers have reached end-of-life (EOL) four years before being discovered, the vendor released a fix at the time in firmware version 2.17b02 along with a security bulletin containing mitigation recommendations.
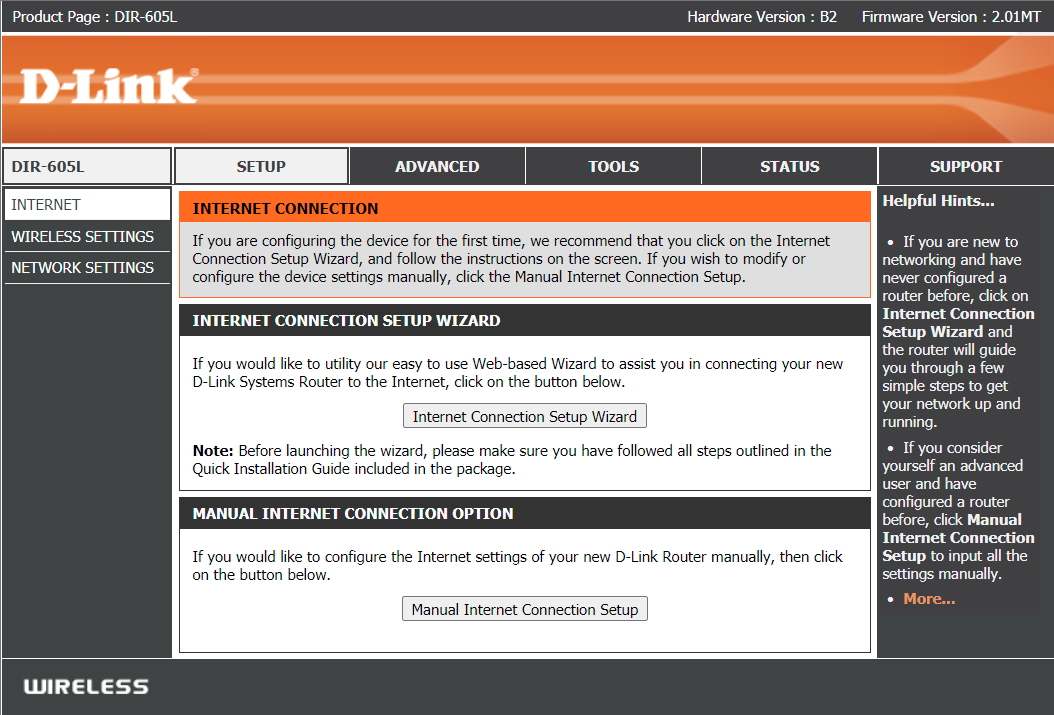
Another bug affecting D-Link products has also been added recently to the KEV catalog. It is identified as CVE-2021-40655 and affects D-Link DIR-605 routers that have been out of support since 2015.
A proof-of-concept exploit for the flaw was released on GitHub in 2021. It demonstrated that an attacker could grab the admin’s username and password via a specially crafted request sent to the /getcfg.php page without authentication.
Source: Github
CISA has not provided any background information about the two D-Link flaws and it is unclear who exploited them or when the agency recorded the attacks.
Older vulnerabilities are typically leveraged by botnet malware that incorporate large lists of exploitable security issues with no regard to the type of device or age of the issue.
In the case of D-Link 600 and 605, it is recommended to replace the device with newer models that the vendor still supports with performance and security updates.









