Tech
New Android malware wipes your device after draining bank accounts

A new Android malware that researchers call ‘BingoMod’ can wipe devices after successfully stealing money from the victims’ bank accounts using the on-device fraud technique.
Promoted through text messages, the malware poses as a legitimate mobile security tool and can steal up to 15,000 EUR per transaction.
According to researchers analyzing it, BingoMod is currently under active development, with its author focusing on adding code obfuscation and various evasion mechanisms to drop detection rate.
BingoMod details
Researchers at Cleafy, an online fraud management and prevention solution, found that BingoMod is distributed in smishing (SMS phishing) campaigns and uses various names that typically indicate a mobile security tool (e.g. APP Protection, Antivirus Cleanup, Chrome Update, InfoWeb, SicurezzaWeb, WebSecurity, WebsInfo, WebInfo, and APKAppScudo).
In one instance, the malware uses the icon for the free AVG AntiVirus & Security tool available on Google Play.
During the installation routine, the malware requests permission to use Accessibility Services, which provides advanced features that allow extensive control of the device.
Once active, BingoMod steals any login credentials, takes screenshots, and intercepts SMS messages.
To perform on-device fraud (ODF), the malware establishes a socket-based channel to receive commands and an HTTP-based channel to send a feed of screenshots, enabling almost real-time remote operation.
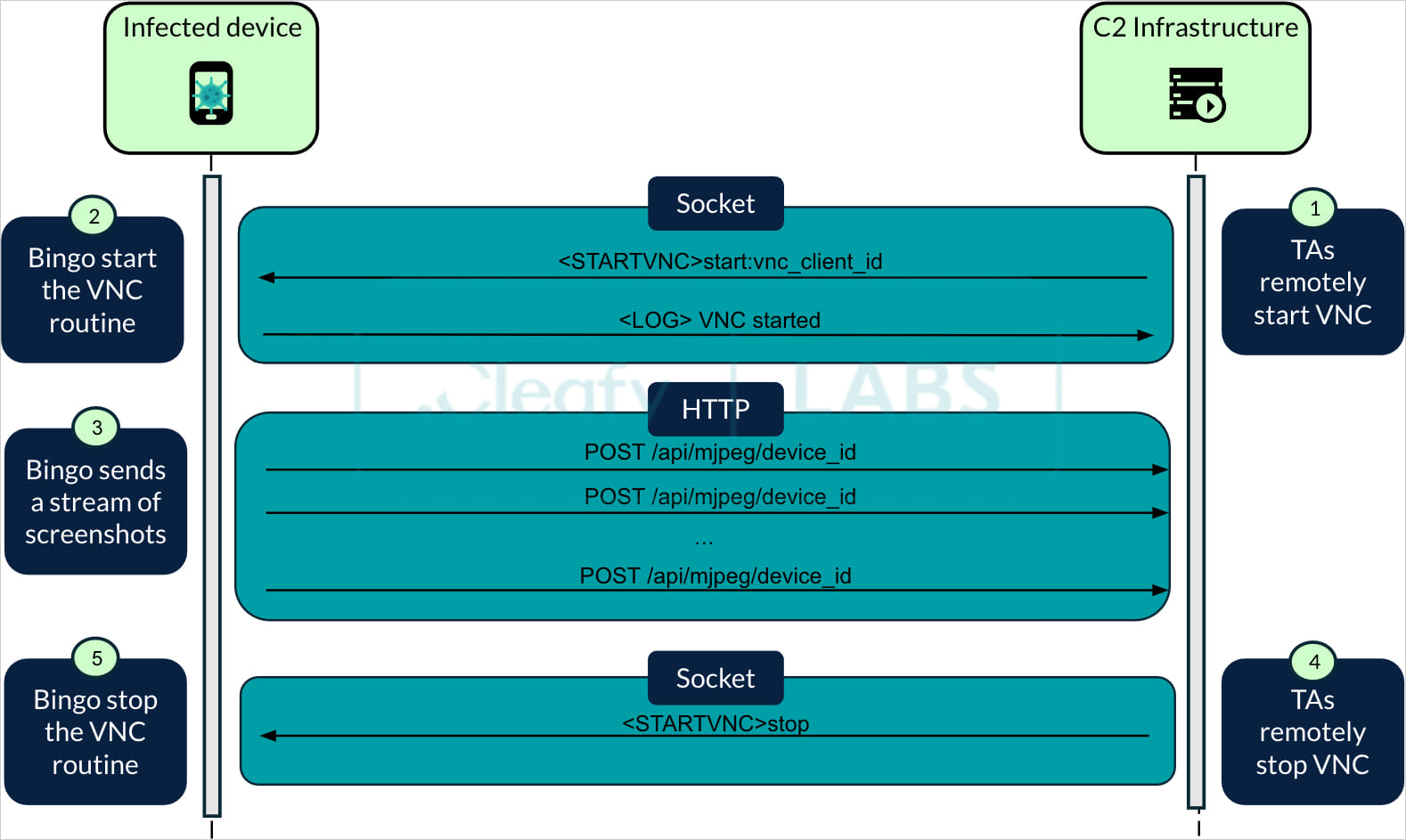
Source: Cleafy
ODF is a common technique used for initiating fraudulent transactions from the victim’s device, which fools standard anti-fraud systems that rely on identity verification and authentication.
Cleafy researchers explain in a report today that “the VNC routine abuses Android’s Media Projection API to obtain real-time screen content. Once received, this is transformed into a suitable format and transmitted via HTTP to the TAs’ [threat actor’s] infrastructure.”
One feature of the routine is that it can leverage Accessibility Services “to impersonate the user and enable the screen-casting request, exposed by the Media Projection API.”

Source: Cleafy
The commands that the remote operators can send to BingoMod include clicking on a particular area, writing text on a specified input element, and launching an application.
The malware also allows manual overlay attacks through fake notifications initiated by the threat actor. Additionally, a device infected with BingoMod could also be used to further spread the malware through SMS.
Disabling defenses and wiping data
BingoMod can remove security solutions from the victim’s device or block activity of apps that the threat actor specifies in a command.
To evade detection, the malware’s creators have added code-flattening and string obfuscation layers, which, based on scan results on VirusTotal, achieved the intended goal.
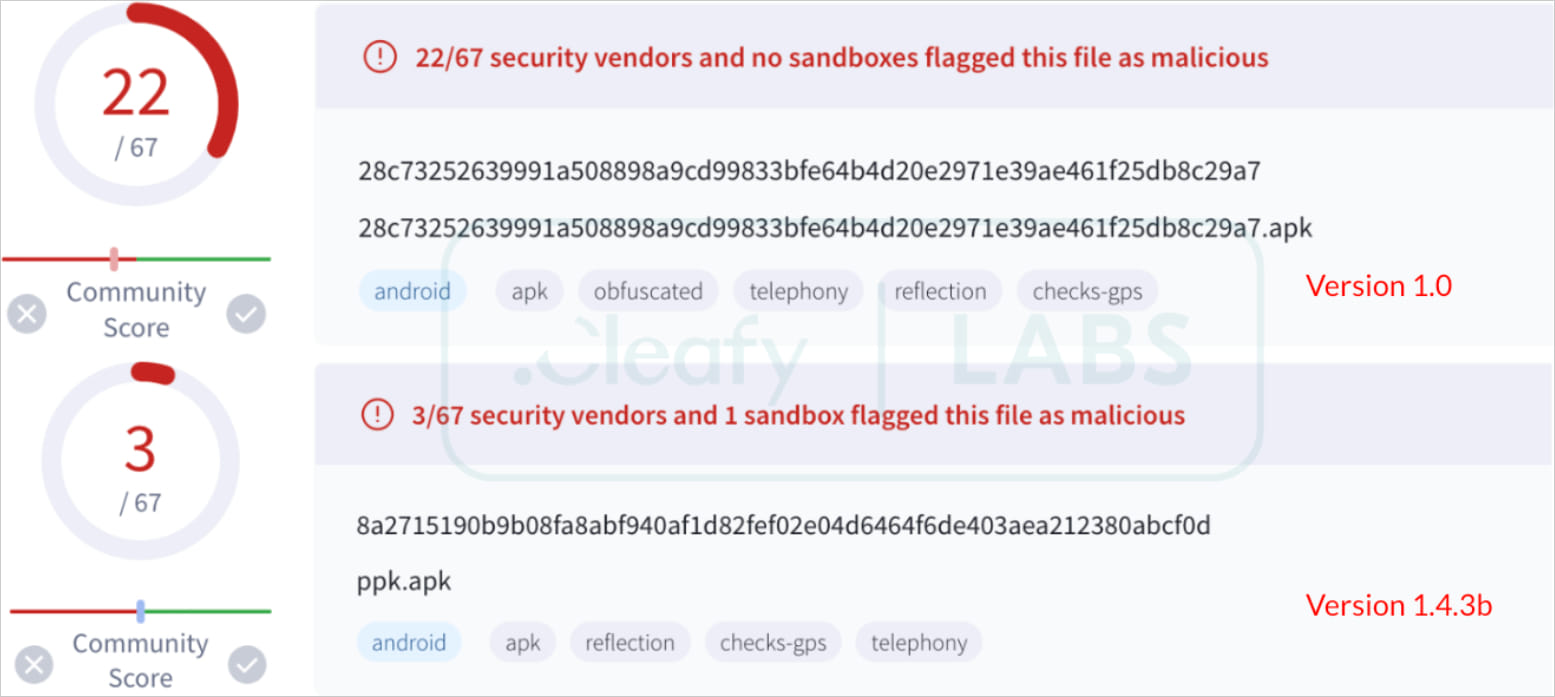
Source: Cleafy
If the malware is registered on the device as a device admin app, the operator can send a remote command to wipe the system. According to the researchers, this function is executed only after a successful transfer and impacts only the external storage.
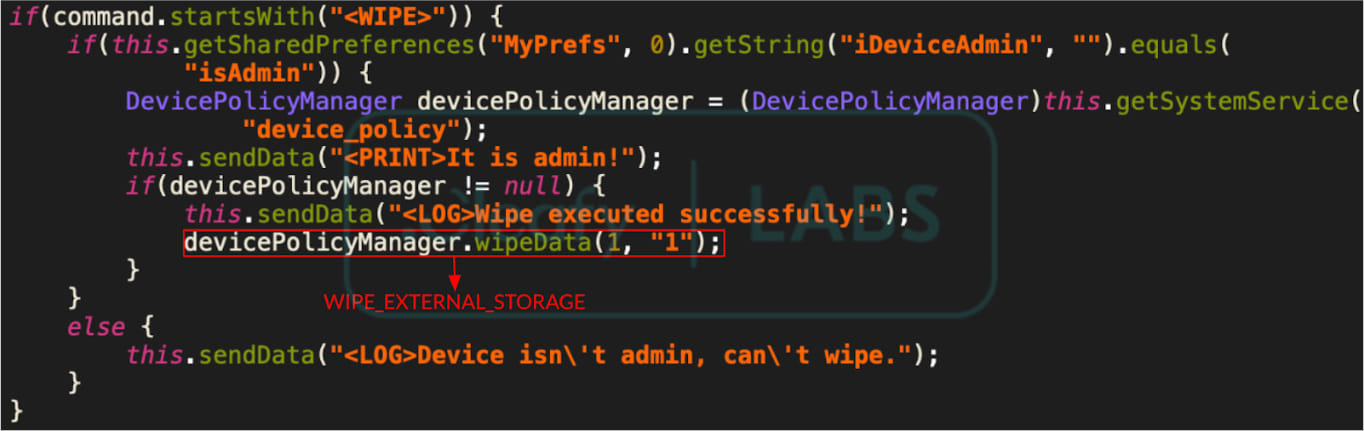
Source: Cleafy
For a complete wipe, it is possible that the threat actor uses the remote access capability to erase all data and reset the phone from the system settings.
Although BingoMod is currently at version 1.5.1, Cleafy says that it appears to be in an early development stage.
Based on the comments in the code, the researchers believe that BingoMod may be the work of a Romanian developer. However, it is also possible that developers from other countries are contributing.









